在企业网络中,企业内部服务器的安全性和保护至关重要。作为企业的核心资产,内网服务器存储了大量敏感数据和机密信息。然而,外部网络的不安全性和威胁一直存在,因此限制外网访问公司内网服务器成为一项重要的任务。通过禁止外网访问,企业可以有效降低网络攻击和数据泄露的风险,保护公司信息资产的完整性和机密性。
本文将重点介绍访问控制列表(ACL),以帮助企业实施外网访问限制策略。通过合理的配置和管理,企业可以确保只有经过授权的人员可以访问内网服务器,为企业网络安全带来更高的保障。只有确保内网服务器的安全性,企业才能更好地应对不断增长的网络威胁,确保业务的连续性和可靠性。
一、关于ACL介绍:
ACL是"Access Control List"(访问控制列表)的缩写。ACL是一种网络安全技术,用于限制或控制对网络资源的访问权限。它定义了哪些用户、设备或网络服务被允许或被禁止访问特定资源。ACL通常应用于网络设备(如路由器、交换机、防火墙)或操作系统中。
ACL基于规则列表的方式工作,每个规则指定了一个或多个条件和相应的操作。条件可以包括源IP地址、目标IP地址、协议类型、端口号、用户身份等。操作则定义了对满足条件的数据包或请求所采取的动作,如允许通过、拒绝或转发。
通过使用ACL,网络管理员可以实施详细的访问控制策略,以保护网络资源的安全性和完整性。它可以用于限制外部网络对内部服务器的访问,阻止特定IP地址或用户访问敏感数据,或者允许特定用户组或应用程序访问特定服务等。
ACL是网络安全中常见的一种控制手段,通过适当配置和管理ACL规则,可以有效地管理和保护其网络资源,降低潜在的安全风险.
二、通过配置ACL策略,来禁止外网访问公司内网服务器
实例要求:
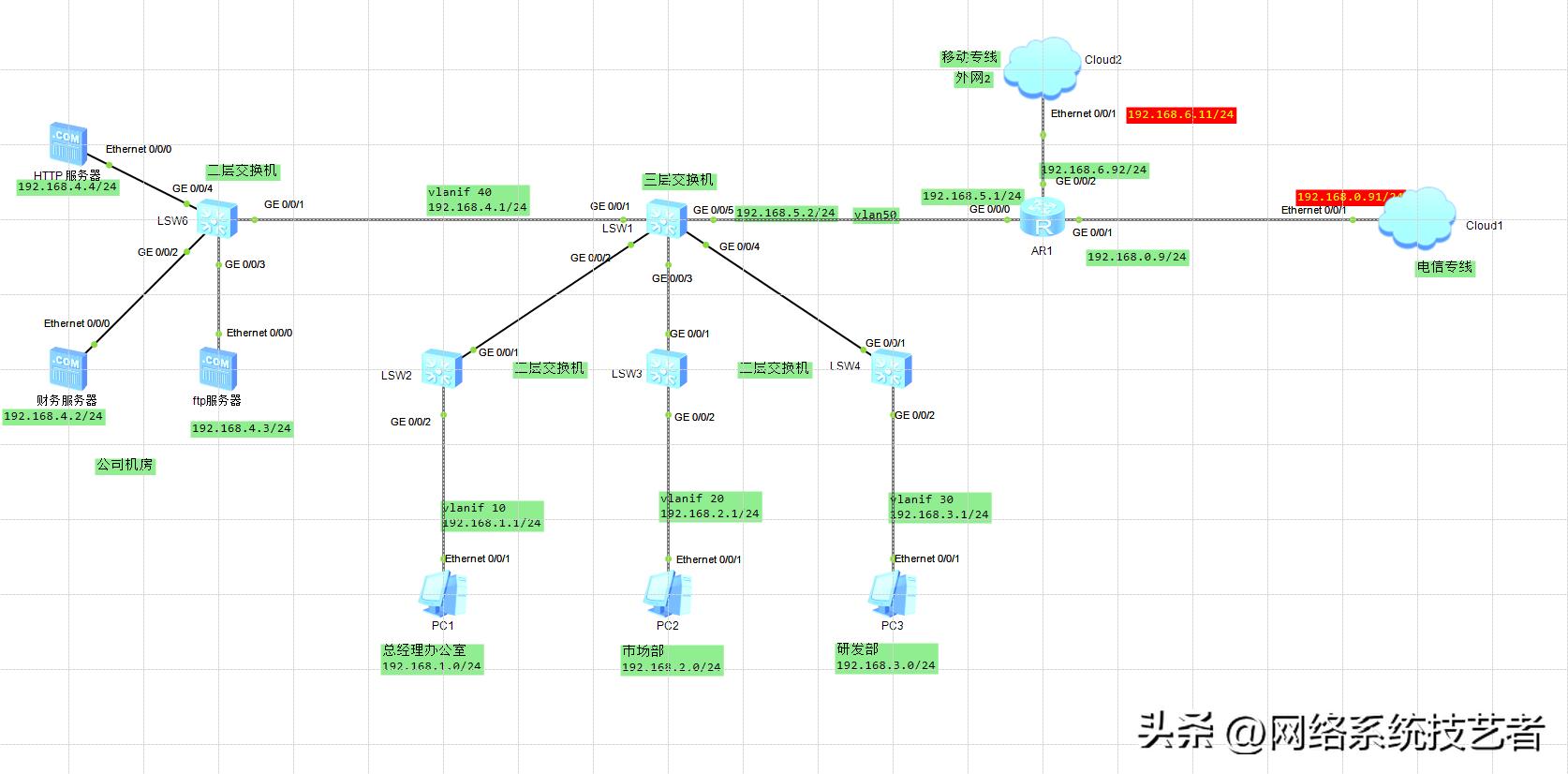
1、公司通过交换机来实现各部门之间的互连
2、现要求只允许总经理办公室用户可以访问内网中的 财务服务器
3、其他部门及外网用户禁止访问。
网络拓扑:
连通性具体配置:
二层交换机配置
#LSW2交换机
The device is running!
<Huawei>
<Huawei>
<Huawei>sys
Enter system view, return user view with Ctrl+Z.
[Huawei]undo inf
[Huawei]undo info-center en
Info: Information center is disabled.
[Huawei]
[Huawei]
[Huawei]
#创建vlan10 -vlan40
[Huawei]vlan batch 10 to 40
Info: This operation may take a few seconds. Please wait for a moment...done.
[Huawei]
#将接口加入到vlan中
[Huawei]interface GigabitEthernet 0/0/2
[Huawei-GigabitEthernet0/0/2]port link-type access
[Huawei-GigabitEthernet0/0/2]port default vlan 10
[Huawei-GigabitEthernet0/0/2]q
[Huawei]
[Huawei]
#设置与三层核心交换机相连的接口为trunk,并设置运行通过vlan10,vlan20,vlan30,vlan40
[Huawei]
[Huawei]interface GigabitEthernet 0/0/1
[Huawei-GigabitEthernet0/0/1]port link-type trunk
[Huawei-GigabitEthernet0/0/1]port trunk allow-pass vlan 10 to 40
[Huawei-GigabitEthernet0/0/1]q
[Huawei]
[Huawei]
#LSW3交换机
#
undo info-center enable
#
vlan batch 10 to 40
#
#
interface GigabitEthernet0/0/1
port link-type trunk
port trunk allow-pass vlan 10 to 40
#
interface GigabitEthernet0/0/2
port link-type access
port default vlan 20
#
#LSW4交换机
[Huawei]
[Huawei]vlan batch 10 to 40
Info: This operation may take a few seconds. Please wait for a moment...done.
[Huawei]
[Huawei]interface GigabitEthernet 0/0/2
[Huawei-GigabitEthernet0/0/2]port link-type access
[Huawei-GigabitEthernet0/0/2]port default vlan 30
[Huawei-GigabitEthernet0/0/2]q
[Huawei]interface GigabitEthernet 0/0/1
[Huawei-GigabitEthernet0/0/1]
[Huawei-GigabitEthernet0/0/1]port link-type trunk
[Huawei-GigabitEthernet0/0/1]port trunk allow-pass vlan 10 to 40
[Huawei-GigabitEthernet0/0/1]q
[Huawei]
三层交换机:
The device is running!
<Huawei>
<Huawei>sys
Enter system view, return user view with Ctrl+Z.
[Huawei]undo inf
[Huawei]undo info-center en
[Huawei]undo info-center enable
Info: Information center is disabled.
[Huawei]
[Huawei]
#创建vlan 接口并配置IP地址
[Huawei]vlan batch 10 to 40
Info: This operation may take a few seconds. Please wait for a moment...done.
[Huawei]
[Huawei]interface Vlanif 10
[Huawei-Vlanif10]ip address 192.168.1.1 24
[Huawei-Vlanif10]q
[Huawei]
#其他接口配置信息如下
#
interface Vlanif20
ip address 192.168.2.1 255.255.255.0
#
#
interface Vlanif30
ip address 192.168.3.1 255.255.255.0
#
interface Vlanif40
ip address 192.168.4.1 255.255.255.0
#
interface Vlanif50
ip address 192.168.5.2 255.255.255.0
#
#配置三层交换机上连接到接入交换机的接口为Trunk模式,并允许相应VLAN通过:
[Huawei]interface GigabitEthernet 0/0/1
[Huawei-GigabitEthernet0/0/1]
[Huawei-GigabitEthernet0/0/1]port link-type trunk
[Huawei-GigabitEthernet0/0/1]port trunk allow-pass vlan 10 to 50
[Huawei-GigabitEthernet0/0/1]
[Huawei-GigabitEthernet0/0/1]q
[Huawei]
[Huawei]
[Huawei]interface GigabitEthernet 0/0/2
[Huawei-GigabitEthernet0/0/2]port link-type trunk
[Huawei-GigabitEthernet0/0/2]port trunk allow-pass vlan 10 to 40
[Huawei-GigabitEthernet0/0/2]q
[Huawei]
[Huawei]interface GigabitEthernet 0/0/4
[Huawei-GigabitEthernet0/0/4]
[Huawei-GigabitEthernet0/0/4]port link-type trunk
[Huawei-GigabitEthernet0/0/4]port trunk allow-pass vlan 10 to 40
[Huawei-GigabitEthernet0/0/4]q
[Huawei]
[Huawei]
[Huawei]interface GigabitEthernet 0/0/3
[Huawei-GigabitEthernet0/0/3]
[Huawei-GigabitEthernet0/0/3]port link-type trunk
[Huawei-GigabitEthernet0/0/3]port trunk allow-pass vlan 10 to 40
[Huawei-GigabitEthernet0/0/3]q
[Huawei]
# 配置与路由器相连的接口
[Huawei]vlan batch 50
Info: This operation may take a few seconds. Please wait for a moment...done.
[Huawei]
[Huawei]
[Huawei]interface GigabitEthernet 0/0/5
[Huawei-GigabitEthernet0/0/5]port link-type access
[Huawei-GigabitEthernet0/0/5]port default vlan 50
[Huawei-GigabitEthernet0/0/5]q
[Huawei]
[Huawei]interface Vlanif 50
[Huawei-Vlanif50]ip ad
[Huawei-Vlanif50]ip address 192.168.5.2 24
[Huawei-Vlanif50]q
[Huawei]
#配置静态路由
[Huawei]
[Huawei]ip route-static 0.0.0.0 0.0.0.0 192.168.5.1
[Huawei]
[Huawei]
# 创建高级ACL 3002并配置ACL规则,允许位于内网的总裁办公室,访问财务服务器的报文通过,拒绝其他部门及外网用户访问财务服务器的报文通过。
[Huawei]acl 3002
[Huawei-acl-adv-3002]rule permit ip source 192.168.1.0 0.0.0.255 destination 192
.168.4.2 0.0.0.0
[Huawei-acl-adv-3002]rule 20 deny ip destination 192.168.4.2 0.0.0.0
[Huawei-acl-adv-3002]q
[Huawei]
#配置基于ACL的流分类,配置流分类c_network,对匹配ACL 3002的报文进行分类。
[Huawei]traffic ?
behavior Configure traffic behavior
classifier Configure traffic classifier
policy Configure traffic policy
[Huawei]traffic clas
[Huawei]traffic classifier c_net
[Huawei]traffic classifier c_network
[Huawei-classifier-c_network]if
[Huawei-classifier-c_network]if-match ac
[Huawei-classifier-c_network]if-match acl 3002
[Huawei-classifier-c_network]
[Huawei-classifier-c_network]q
[Huawei]
#配置流行为b_network,动作为允许报文通过(缺省值,不需配置)
[Huawei]traffic behavior b_network
[Huawei-behavior-b_network]
[Huawei-behavior-b_network]q
[Huawei]
# 配置流策略p_network,将流分类c_network与流行为b_network关联。
[Huawei]traffic po
[Huawei]traffic policy p_network
[Huawei-trafficpolicy-p_network]
[Huawei-trafficpolicy-p_network]clas
[Huawei-trafficpolicy-p_network]classifier c
[Huawei-trafficpolicy-p_network]classifier c_net
[Huawei-trafficpolicy-p_network]classifier c_network b
[Huawei-trafficpolicy-p_network]classifier c_network behavior b_network
[Huawei-trafficpolicy-p_network]
[Huawei-trafficpolicy-p_network]q
[Huawei]
#应用流策略
Huawei]interface GigabitEthernet 0/0/1
[Huawei-GigabitEthernet0/0/1]tra
[Huawei-GigabitEthernet0/0/1]traffic-?
traffic-filter traffic-limit
traffic-mirror traffic-policy
traffic-pppoe traffic-redirect
traffic-remark traffic-statistic
[Huawei-GigabitEthernet0/0/1]traffic-p
[Huawei-GigabitEthernet0/0/1]traffic-policy p_netw
[Huawei-GigabitEthernet0/0/1]traffic-policy p_network
[Huawei-GigabitEthernet0/0/1]traffic-policy p_network out
[Huawei-GigabitEthernet0/0/1]traffic-policy p_network outbound
[Huawei-GigabitEthernet0/0/1]q
[Huawei]
路由器配置
The device is running!
####################################
<Huawei>
May 30 2023 10:56:23-08:00 Huawei %%01IFPDT/4/IF_STATE(l)[0]:Interface GigabitEt
hernet0/0/0 has turned into UP state.
<Huawei>
May 30 2023 10:56:23-08:00 Huawei %%01IFPDT/4/IF_STATE(l)[1]:Interface GigabitEt
hernet0/0/1 has turned into UP state.
<Huawei>
<Huawei>sys
Enter system view, return user view with Ctrl+Z.
[Huawei]undo inf
[Huawei]undo info-center en
Info: Information center is disabled.
[Huawei]
[Huawei]
[Huawei]interface GigabitEthernet 0/0/0
[Huawei-GigabitEthernet0/0/0]ip address 192.168.5.1 24
[Huawei-GigabitEthernet0/0/0]q
[Huawei]
[Huawei]
[Huawei]int
[Huawei]interface gi
[Huawei]interface GigabitEthernet 0/0/1
[Huawei-GigabitEthernet0/0/1]ip add
[Huawei-GigabitEthernet0/0/1]ip address 192.168.0.9 24
[Huawei-GigabitEthernet0/0/1]q
[Huawei]
[Huawei]interface GigabitEthernet 0/0/2
[Huawei-GigabitEthernet0/0/2]ip address 192.168.6.92 24
[Huawei-GigabitEthernet0/0/2]q
[Huawei]
[Huawei]ip route-static 0.0.0.0 0.0.0.0 192.168.0.91
[Huawei]
[Huawei]ip route-static 0.0.0.0 0.0.0.0 192.168.6.11
[Huawei]ip route-static 192.168.0.0 255.255.0.0 192.168.5.2
[Huawei]
#创建ACL访问控制列表
[Huawei]
[Huawei]acl number 2001
[Huawei-acl-basic-2001]rule 5 permit source 192.168.0.0 0.0.255.255
[Huawei-acl-basic-2001]q
[Huawei]
[Huawei]interface GigabitEthernet 0/0/1
[Huawei-GigabitEthernet0/0/1]nat outbound 2001
[Huawei-GigabitEthernet0/0/1]
[Huawei-GigabitEthernet0/0/1]q
[Huawei]
[Huawei]interface GigabitEthernet 0/0/2
[Huawei-GigabitEthernet0/0/2]nat outbound 2001
[Huawei-GigabitEthernet0/0/2]q
[Huawei]
测试:
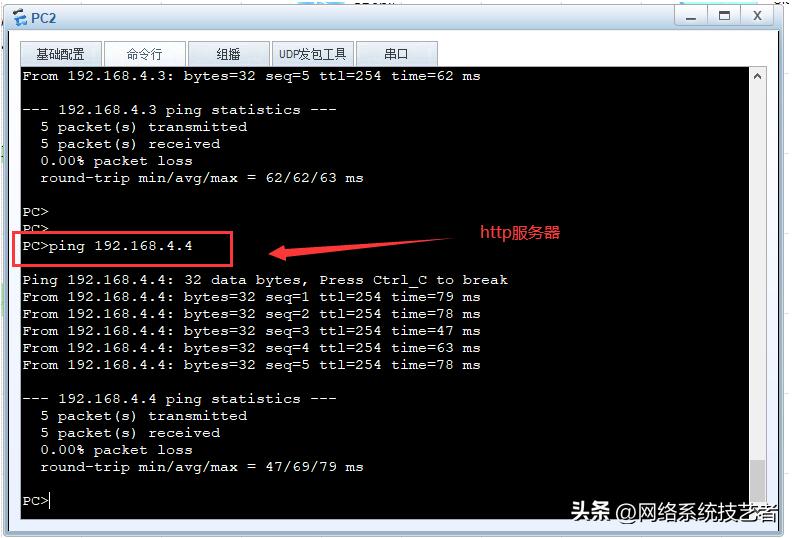
1、PC主机能够ping 通两条外网专线
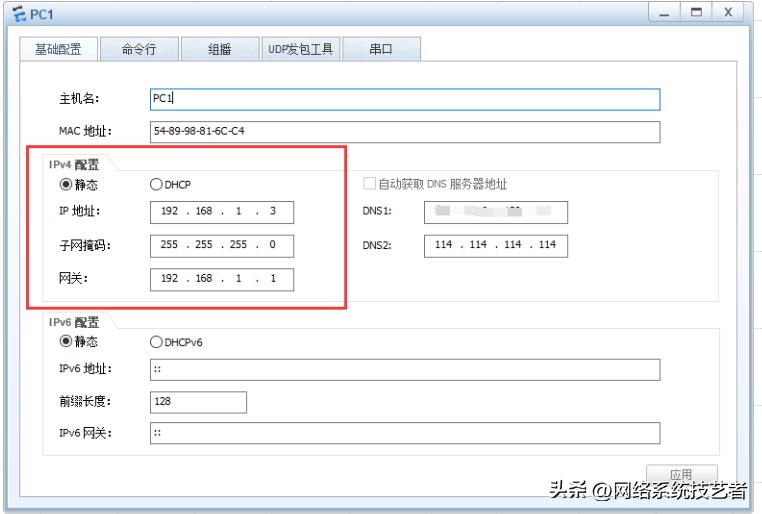

2、总经理办公室能够访问财务服务器,其他部门的pc 主机不能访问,但是其他部门的pc 主机能够访问除了财务服务器之外的其他服务器。


至此,本实验结束。
写在最后:
自我设限,固步自封,唯有突破极限,才能发掘潜能。以上就是本期整理的《公司内部服务器,如何通过ACL 来控制,公司内部及外部用户的访问》,自己经历过的风雨,所以知道你也会坚强。你的【点赞】+【关注】,我会自动解读为认可。
作者简介:
我是“网络系统技艺者”,系统运维工程师一枚,持续分享【网络技术+系统运维技术】干货。码字不易,如果您觉得文章还可以,就收藏吧,也许在以后某个时间能够用得到。